Real World Crypto: Day 1 posted January 2016
Everyone was at CCC before new years eve, and everyone keeps talking about how great it was and how good a time they had... :(
But now is RWC2016 (nothing to do with the real world cup)! and it's awesome! and it's so far the best crypto convention I've attended!

Global overview and dumb summary of the day (followed by notes of the talks, so just skip this list):
- one big room composed of around 400-500 people in the middle of Stanford university
- it's raining, locals are happy, we are not
- talks of various times (10-40min) chained, on many different topics
- awkwardly meeting people
- free food (and great food!) and starbucks coffee (I think I'm the only one happy about that) and cypher wine

- 12 talks, only 1 girl
- every one in cryptography is here (diffie, rivest, watson ladd, boneh, djb, tanja, phong nguyen, lochter, trevor perrin, filippo, tancrede lepoint...)
09:30 - The Blackphone
tl;dw: marketing speech
Two human beings verbally compare the Short Authentication String, drawing the human brain directly into the protocol. And this is a Good Thing.
ZRTP seems to be a normal DH key exchange, except that you have to compare SAS (a hash) of the public keys aloud on the phone.
There is also the concept of key continuity, where you keep some value that will be used in the following DH key exchange.
If the MiTM is not present in the first call, he is locked out of subsequent calls
Makes me think, why the ratchet in Axolotl? Why the need to constantly change the key being used to encrypt? If someone knows the answer :)
- "don't let cryptographers design UX"
- the password is generated from their server and handed to the user... they say they don't want user to generate weak password. WTF
- encrypted dB -> they removed it because it was annoying people. WTF
- they replaced AES, sha2, etc... with "non-NIST" suite (twofish, ...) that comes from NIST funded competitions. WTF
- they used tanja and bernstein gifted curve (41417). They wanted a unique curve. WTF
- tanja asks a question (missed it), he answers "post-quantum right now is marketing". Haha
10:00 - Cryptographic directions in Tor: past and future
tl;dw: not much crypto at first, now crypto, in the future more weird crypto?
- they took a crypto class in 2004 and chose the ciphersuite for Tor from that -> AES-CTR, truncated sha1, plenty of bad decisions
- key negociation: RSA1024 + DH1024 + AES-CTR (no name, then they called it "TAP")
- links? they used TLS 1.0 (a link is the connection between two relays)
- they replaced a lot of it now
- key negociation: curve25519 + sha256 (called "ntor")
- tls >= 1.0, with ecdh (P256)
- work remains:
- truncated sha1 is too malleable
- not enough post quantum (and people are scared of that)
- need to remove rsa1024
- AES-CTR is malleable, MAC allows tagging attacks if first and third relays are evil -> woot?
Here's a blogpost from Tom Ritter about tagging attacks. The idea: the first node XOR some data to the ciphertext, the third node sees the modified data in clear (if the data is not going through https). So with two evil nodes, being the first and last, you can know who is visiting what website (traffic correlation).
There was also something about doing it with the sha1, and something about adding a MAC between each relay. But I missed that part, if someone can fill in the blanks for me?
-
they want to use AEZ in the future (rogaway)? or HHFHFH? (djb)
- This is scary as many have stated. Djb said "crypto should be boring" (at least I heard he said that), and he's totally right. Or at least double encrypt (
AES(AEZ(m))) - AEZ is an authenticated cipher (think AES-GCM or chacha20-poly1305) that is part of the CAESAR competition
- HHFHFH is ...? No idea, if someone knows what Nick is talking about?
- This is scary as many have stated. Djb said "crypto should be boring" (at least I heard he said that), and he's totally right. Or at least double encrypt (
- Nick talks about newhope as well (I presume he's talking about this post-quantum key exchange?). He wants more post-quantum stuff in his thing.
10:20 - Anonize: An anonymous survey system
tl;dw: how to do an anonymous survey product with a nice UX (paper is here)
- problems of a surveys:
- you want authenticity (only authorized users, only one vote per person)
- anonymity (untracable response)
- surveymonkey (6% of the survey online):
- they don't care about double votes
- special URLs to trace responses to single users/groups
- anyone who infiltrate the system can get that info
- they do everything wrong
- Anonize overview
- 1) you create a public key
- 2) create survey, unique URL for everyone
- 3) you fill out something, you get a QR code
- what you submit is a [response, token] with the token a ZK proof for... something.
- they will publish API, and it's artistic
The talk was mostly spent on showing how beautiful the UX was. I would have prefered something clearer on how the protocol was really working (but maybe other understood better than me...)
11:10 - Cryptography in AllJoyn, an Open Source Framework for IoT
tl;dw: the key exchange protocol behind their AllJoyn, the security of devices that uses this AllJoyn api/interface...
What's AllJoyn? Something that you should use in your IoT stuff apparently:
AllJoyn is an open source software framework that makes it easy for devices and apps to discover and communicate with each other. Developers can write applications for interoperability regardless of transport layer, manufacturer, and without the need for Internet access. The software has been and will continue to be openly available for developers to download, and runs on popular platforms such as Linux and Linux-based Android, iOS, and Windows, including many other lightweight real-time operating systems.
- they want security to be the same whatever they use (tcp, udp, ip, bluetooth, etc.) so they created their own TLS-like protocol with way less options
- EC-SPEKE will replace PSK
- key exchange overview (~4 round trips to derive a session key, outch!)
- ECHDE_ECDSA key exchange
- devices are in "claimable" state when they join the network
- they get assigned a cert/policy by the security manager
- policy reffers to level of access/control
- app has a "manifest" of interfaces it wants to use (like facebook permissions)
- security manager has a change to see that and accept/refuse it
- they get assigned a cert/policy by the security manager
...
11:40 - High-assurance Cryptography
tl;dw: they have open source code to formaly verify cryptographic implementations
- they (Galois) have tools since 99 to verify crypto, using SMT solver, SAT solver, etc.
- acts as a compiler (from the user's point of view)
- everything he's talking about is open source:
- Cryptol, functionnal language. cryptol.net
- SAW The Software Assurance Workbench
SAW supports analysis of programs written in C, Java™, MATLAB®, and Cryptol, and uses efficient SAT and SMT solvers such as ABC and Yices.
https://galois.com/project/software-analysis-workbench/
- Verification engineers can use SAW to prove that a program implements its specification.
- Security analysts can have SAW generate models identifying constraints on program control flow to identify inputs that can reach potentially dangerous parts of a program.
- Cryptographers can have SAW generate models from production cryptographic code for import and use within Cryptol.
- takes to 10-100 minutes to verify a crypto primitive
- if you have a high formulation of your algorithm, why not make it write code?
12:00 - The first Levchin prize for contributions to real-word cryptography
tl;dw: dude with a lot of money decides to give some to influencal cryptographers every year, also gives them his name as a reward.
The Levchin prize honors significant contributions to real-world cryptography. The award celebrates recent advances that have had a major impact on the practice of cryptography and its use in real-world systems. Up to two awards will be given every year and each carries a prize of $10,000.
$10,000, twice a year. It's the first edition. Max Levchin is the co-founder of paypal, he likes puzzles.
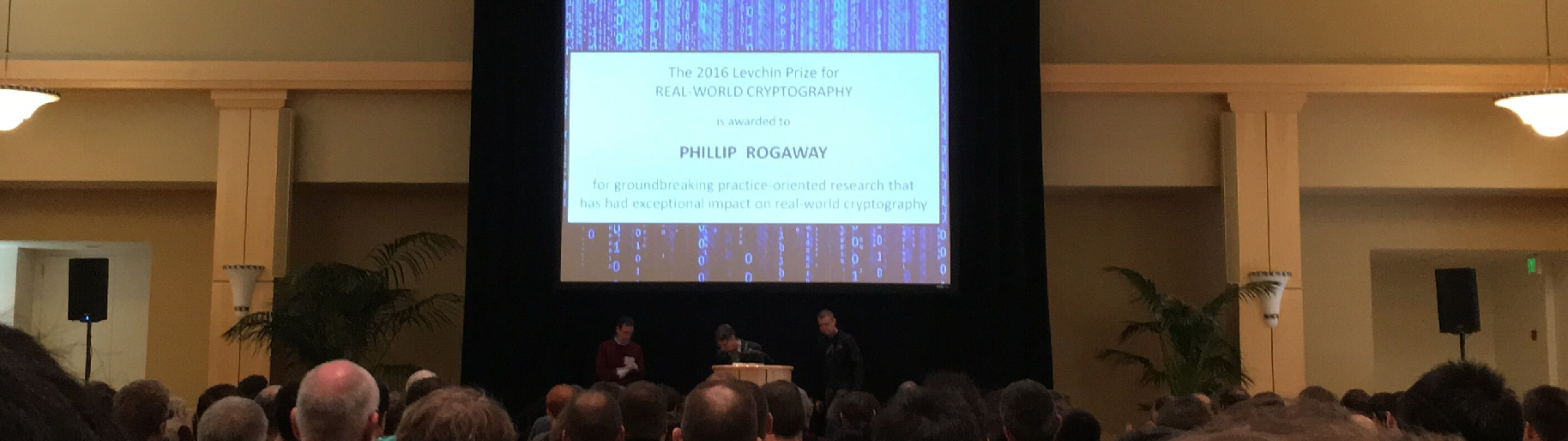
- first prize is awarded to Phillip Rogaway (unanimously) -> concrete security analysis, authenticated encryption, OCD, synack, format-preserving encryption, surveillance resistance crypto, etc. Well the guy is famous.
- second award goes to several people from INRIA for the miTLS project (Karthikeyan Bhargavan, Cedric Fournet, Markulf Kohlweiss, Alfredo Pironti). Well deserved.
14:00 - PrivaTegrity: online communication with strong privacy
tl;dw:
Well. David Chaum, Privategrity: "A wide range of consumer transcations multiparty/multijurisdiction -- efficientyl!"
I won't comment on that. Everything is in these slides:
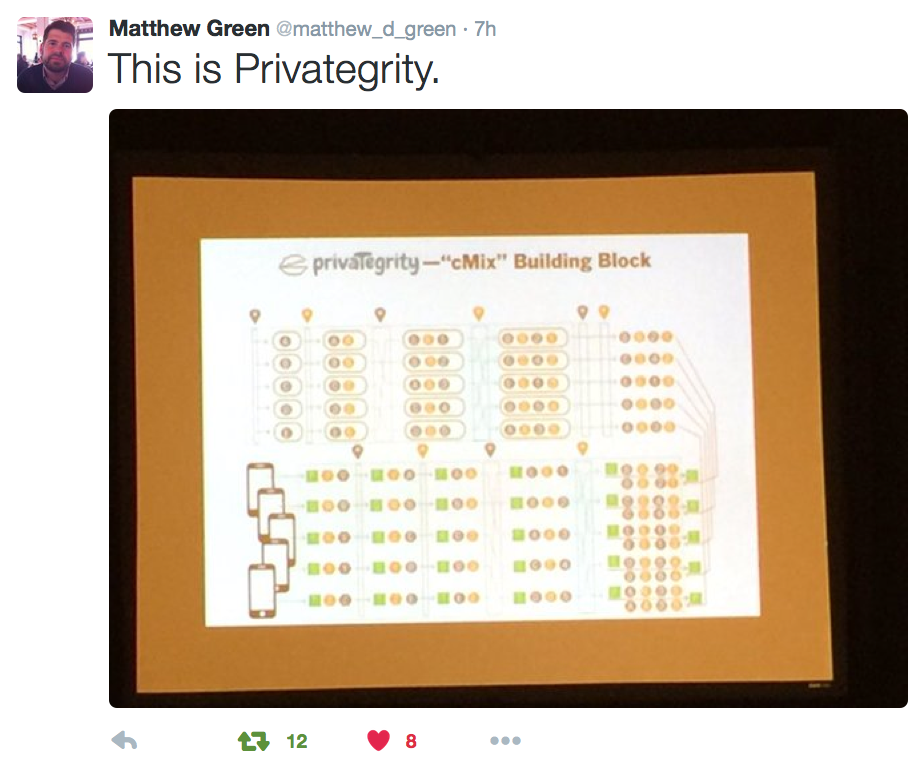

I mean seriously, if you use slides like that, and talk really loud, people will think you are a genius? Or maybe the inverse. I'm really confused as to why that guy was authorized to give a talk.
More comments here: https://news.ycombinator.com/item?id=10850192
14:30 - Software vulnerabilities in the Brazilian voting machine
tl;dw: br voting machine is a shitstorm
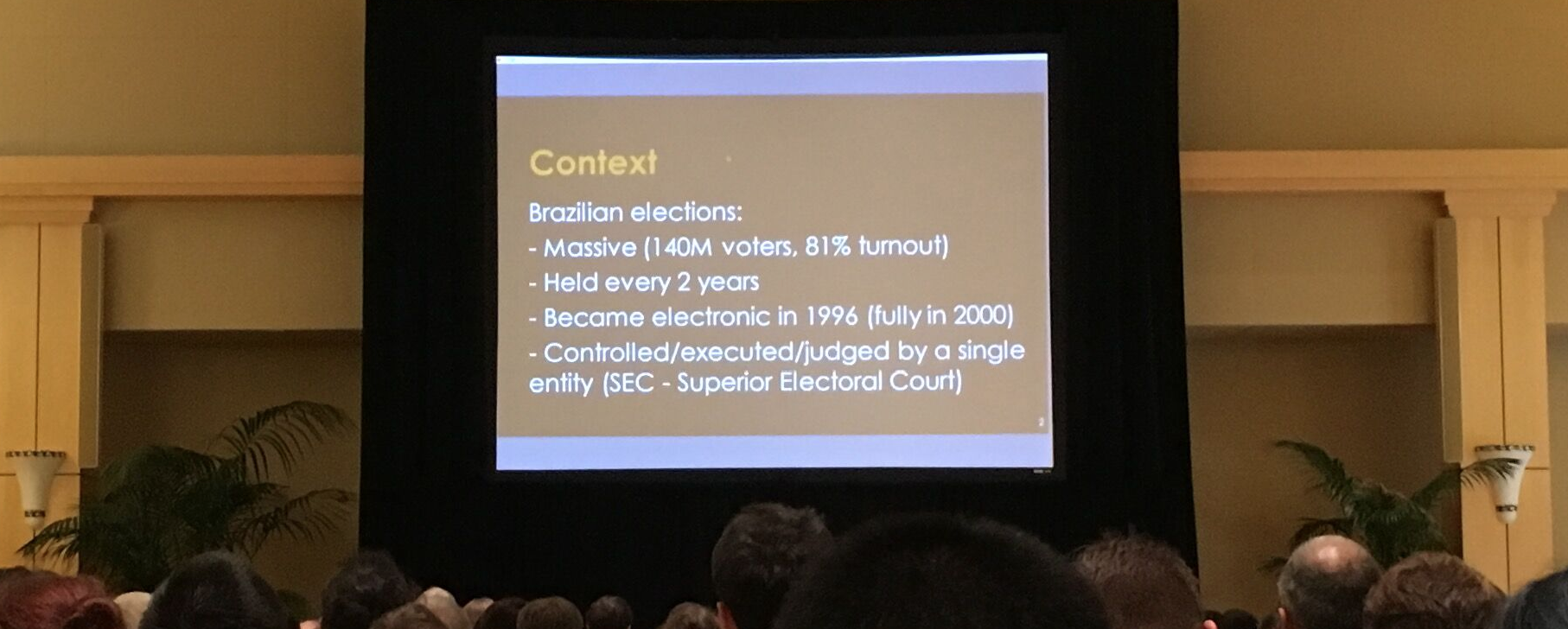
A direct-recording electronic (DRE) voting machine records votes by means of a ballot display provided with mechanical or electro-optical components that can be activated by the voter (typically buttons or a touchscreen); that processes data by means of a computer program; and that records voting data and ballot images in memory components. After the election it produces a tabulation of the voting data stored in a removable memory component and as printed copy. The system may also provide a means for transmitting individual ballots or vote totals to a central location for consolidating and reporting results from precincts at the central location. The device started to be massively used in 1996, in Brazil, where 100% of the elections voting system is carried out using machines. In 2004, 28.9% of the registered voters in the United States used some type of direct recording electronic voting system, up from 7.7% in 1996.
- 13 millions LOC. WTF
- 1) print zero tape first to prove no one has voted (meaningless)
- 2012, gov organized an open contest to find vulns in the system (what he did), extremly restricted, just a few hours, no pen/paper
- he found hardcoded keys in plain sight
- gov says it's a "voting software that checks itself" (what does it mean? canary in the assembly code? Complety nonsense and non-crypto)
- he tried a
grep -r rand *and...- got a match in a file:
srand(time(NULL)) - this is predictible if you know the time, and they know the machines are launched between 7 and 8am. Bruteforce?
- the time is actually public, no need for brute force...
- gov asked if hashing the time would work, no? Well hashing the time twice then?
- finally fixed by using
/dev/urandomalthough the voting machines have two hardware RNGs
- got a match in a file:
- YouInspect: initiative, take pictures of the vote ticket, upload it (didn't get what was the point of that, didn't seem to yield any useful results)
14:50 - The State of the Law: 2016
tl;dw: blablabla
15:50 - QUIC Crypto
- the only talk with very few slides. Adam Langley only used them when he needed pedagogical support. This is brilliant.
- forward secure part of QUIC is better than forward secure in TLS (how? Didn't get that)
- QUIC crypto will be replaced by TLS 1.3
- QUIC will go on, but TLS works over TCP so they will have to make some changes?
There was this diagram where a client would send something to the server, if he didn't have the right ticket it wouldn't work, otherwise it would work... If you understood that part please tell me :)
16:20 - On the Security of TLS 1.3 and QUIC Against Weaknesses in PKCS#1 v1.5 Encryption
- most used tls version is 1.0 (invented in 1999, when windows 98 was the most used OS)
- pkcs#1 v1.5 is removed from tls 1.3
- the bleichenbacher attack on pkcs#1 v1.5 is still possible.... attack explained here (the thing works if you have a server which supports both 1.3 and older versions)
- idea of a solution?: use different certificates for 1.3 and 1.0
Someone from the audience: "no cool name and logo?"
16:40 - The State of Transport Security in the E-Mail Ecosystem
10 minutes of (painful) talk (but good job nonetheless Aaron: you went through to the end).
paper is here if you're interested: http://arxiv.org/pdf/1510.08646v2.pdf
16:50 - Where the Wild Warnings Are: The TLS Story
tl;dw: users get certificate errors browsing the net because their clock is not correct.
- users are getting used to errors, and tend to dismiss them
- making stats of errors warning to users:
- 51% of warnings are non-overridable
- 41% of warnings are for facebook, youtube, google (because they are "portals to the web")
- errors come from the client:
- client clock misconfiguration (61%)
- they have an error for that that allows you to fix your clock on android
- can't send messages on whatsapp because of this problem as well
- captive portals
- security products
- ...
- client clock misconfiguration (61%)
- errors come from the server:
- government has tons of errors with weird certificates
- ...
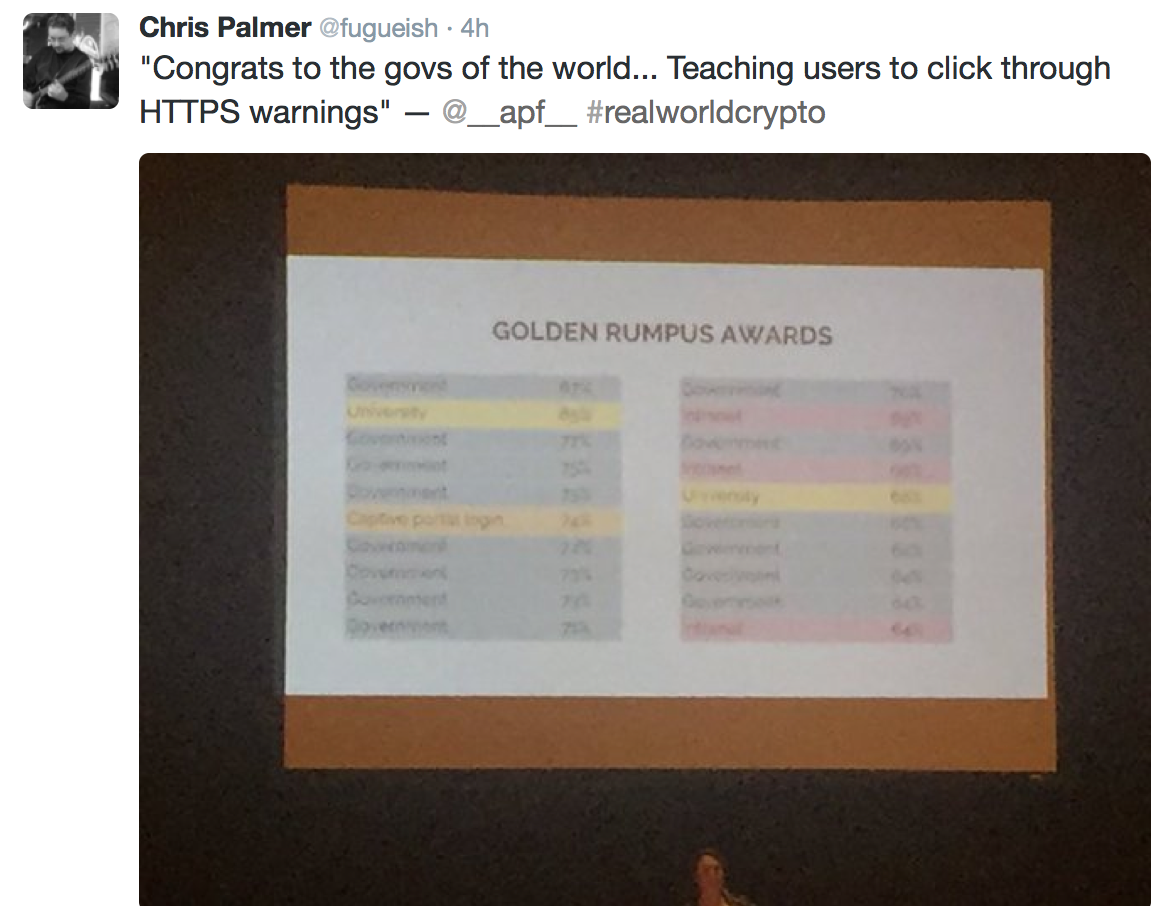
Someone in the public is suggesting that this is because the governments are trying to teach people to ignore these errors (obviously joking). Another one is saying that they might want users to add their "special certificate". Because it can overrides HSTS on rogue certificates. Don't know if this is true. But I'm thinking, why not add certificates for only the website that requests it. Like a certificate jail. Or maybe save the certificate in a different "user-added" folder, websites being signed by certificates from this folder would make chrome display "this website is signed by a certificate you added. If you think this is not normal blablabla".
APF is talking about how they are scared that users will get desensitized by errors, but why display errors? Why not just display a warning. That would annoy real servers and oblige them to get their certs in order, that would make the users suspicious but not unable to access their website (and to google for solutions like "just add the certificates in your root store").
Watson Ladd (that the host recognized) asked her how far from the real time the clock were setup. He thought maybe it could be the battery killing the laptop, NTP not working right away (I missed why) and so the time difference would be negative. In my understanding the clock difference was causing a problem because of certificates notBefore or notAfter fields, so that wouldn't be a problem.
Also people are wondering why these clocks are different, if they should fix it for the user? But maybe not since it might be that the user want his clock to be incorrect... I just remember a time when I would purposely modify the time so that I could keep using my time limited trials (photoshop?).


Comments
Joe Kiniry
Great quick writeup. Thanks for that!
Joe
Diego Aranha
Great coverage of the talks! A minor comment on the "software check itself" issue. Still nonsensical, but the voting software checks the hashes of its own files at boot time. :)
There are lots of other details in https://sites.google.com/site/dfaranha/projects/report-voting.pdf
Thanks!
david
Thanks for the precision Diego! I was wondering what it meant. So I guess this is non-sense because you can just remove this check if you can modify the program
Francis Kim
Nothing about Bitcoin... which is good for a change! Great summary :)
Lewis Etheridge
David Chaum is one of the greatest computer and cryptography men that ever lived. People just do not understand what he is doing. He lead the ONR to develop TOR and then the Admirals released it to cover agents comms worldwide It works well but if David Chaum says he has an end to Crypto wars bet your ass he does. I have been in Communications and Intelligence for 49 years and I have never seen David Chaum fail at anything. He is Crypto. Other than a couple of systems like Chao II which is very good. How many of you can pull 1098 encryption at all times?
I would like to here from you.
Lewis E
david
I'll just say that you probably had the greatest mind in crypto gathered up in that room, and I couldn't find anyone who understood David Chaum's talk.
leave a comment...