Alternatives to PGP posted May 2020
As part of my book's chapter on end-to-end encryption I've been writing about the horrors of PGP.
As a recap of what's bad with PGP:
- No authenticated encryption. This is my biggest issue with PGP personally.
- Receiving a signed message means nothing about who sent it to you (see picture below).
- Usability issues with GnuPG (the main implementation).
- Discoverability of public keys issue.
- Bad integration with emails.
- No forward secrecy.
For more, see my post on a history of end-to-end encryption and the death of PGP.
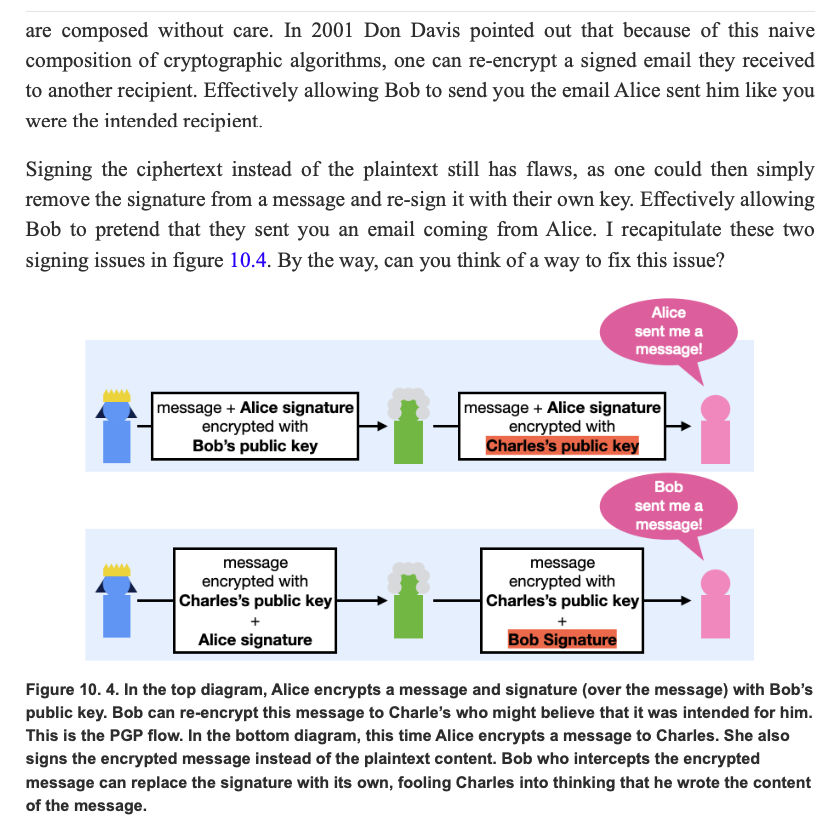
(excerpt from the book Real World Cryptography)
The latter two I don't care that much. Integration with email is doomed from my point of view. And there's just not way to have forward secrecy if we want a near-stateless system.
Email is insecure. Even with PGP, it’s default-plaintext, which means that even if you do everything right, some totally reasonable person you mail, doing totally reasonable things, will invariably CC the quoted plaintext of your encrypted message to someone else (we don’t know a PGP email user who hasn’t seen this happen). PGP email is forward-insecure. Email metadata, including the subject (which is literally message content), are always plaintext. (Thomas Ptatcek)
OK so what can I advise to my readers? What are the alternatives out there?
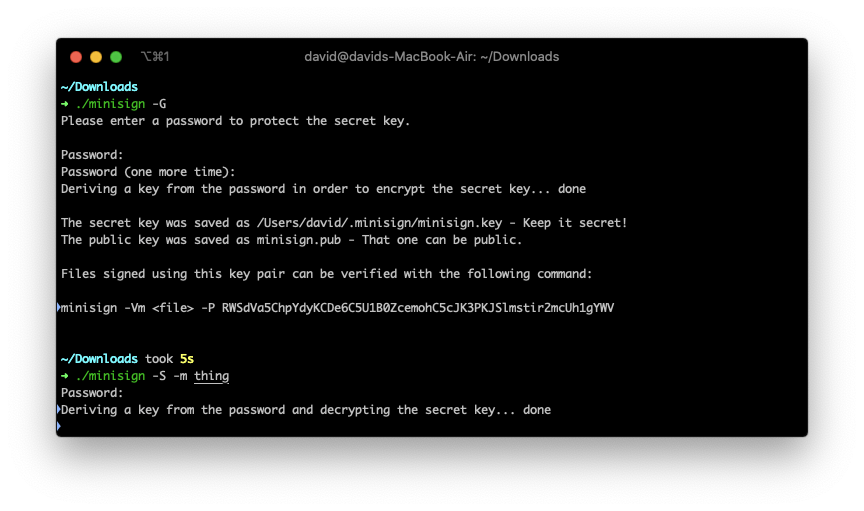
For file signing, Frank Denis wrote minisign which looks great.
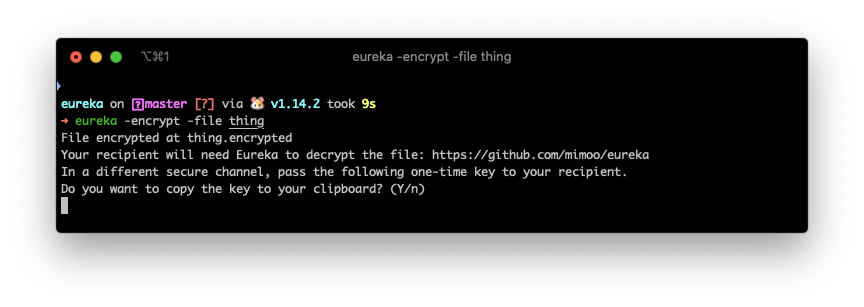
For file encryption, I wrote eureka which does the job. There's also magic wormhole which is often mentioned, and does some really interesting cryptography, but does not seem to address a real use-case (in my opinion) for the following reason: it's synchronous. We already have a multitude of asynchronous ways to transfer files nowadays (dropbox, google drive, email, messaging, etc.) so the problem is not there. Actually there's really no problem... we just all need to agree on one way of encrypting a file and eureka does just that in a hundred lines of code.
(There is a use-case for synchronous file transfer though, and that's when we're near by. Apple's airdrop is for that.)
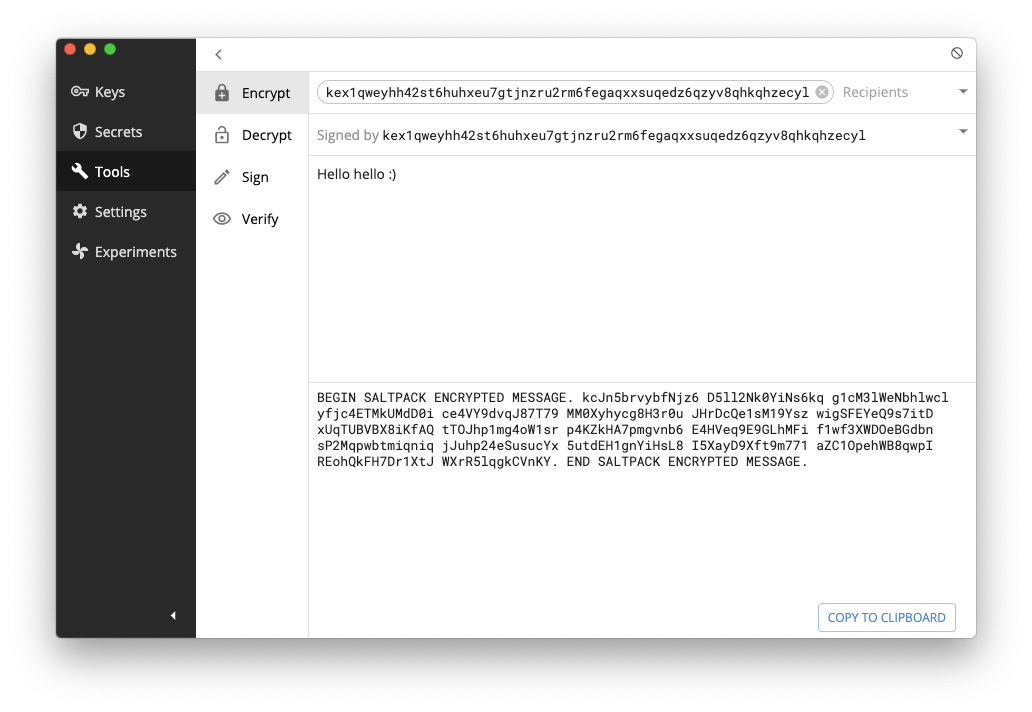
For one-time authenticated messaging (some people call that signcryption) which is pretty much the whole use-case of PGP, there seems to be only one contender so far: saltpack. The format looks pretty great and seems to address all the issues that PGP had (except for forward secrecy, but again I don't consider this a deal breaker). It seems to only have two serious implementations: keybase and keys.pub. Keybase a bit more involved, and keys.pub is dead simple and super well put. Note that age and rage (which are excellent engineering work) seem to try to address this use case. Unfortunately they do not provide signing as Adam Caudill pointed out. Let's keep a close eye on these tools though as they might evolve in the right direction. To obtain public keys, the web of trust (signing other people keys) hasn't been proven to really scale, instead we are now in a different key distribution model where people broadcast their public keys on various social networks in order to instill their identity to a specific public key. I don't think there's a name for it... but I like to call it broadcast of trust.
For encrypted communications, Signal has clearly succeeded as a proprietary solution, but everyone can benefit from it by using other messaging apps like WhatsApp and Wire or even federated protocols like Matrix. Matrix' main implementation seems to be Riot which I've been using and really digging so far. It also looks like the French government agrees with me. Same thing here, the web of trust doesn't seem to work, and instead what seems to be working is relying on centralized key distribution servers and TOFU but verify (trust the first public key you see, but check the fingerprint out-of-band later).



Comments
diafygi
Is it possible to add a section on alternatives to the Web of Trust feature of PGP? Being able to sign others' keys and create a decentralized social connection system is super nice for small groups of people.
david
I guess my last point is that if you want encrypted communications, and being able to verify people, you should use things like Signal and Matrix which are much more usable than the WoT.
So far I haven't seen WoT-based applications that did it well enough (I had one in mind but never finished writing it :D maybe one day)
@ppafin
Check this out: https://youtu.be/8vG88mvLbHs No Android, no iOS. @ppafin
Valdo
Strange, my post was cut and the 1st half posted twice. Here follows part II.
... The GPG Suite for Mac is fine, especially because it can encrypt text within a file and it's not necessary to encrypt the file itself (example: encrypt text in an Apple Note works marvellous). The problem is that there is no counterpart for iOS.
Found yesterday the SimpleumSafe; a German app for Mac and iOS, but seems that nobody knows details how exactly this works (if is phoning files or keys home) or if the company keeps some universal decryption key...
david
the problem with GPG is that it's currently broken for a number of reasons (see chapter 10 in real world cryptography)
pepa65
When looking at Eureka's code, I noticed you're always using 0x010101010101010101010101 as the nonce value for every operation. Does it not matter?
david
pepa65: since we always use a different key it does not matter :) but good question
Mike
Why not cover X.509 certificate based S/MIME? It's the traditional alternative to PGP
leave a comment...