Scott Aaronson found a 1994 issue of Cryptolog an internal newsletter at the NSA. He's quoting funny extracts from one of its article about a field trip at the 1992 Eurocrypt Conference.
Those of you who know my prejudice against the “zero-knowledge” wing of the philosophical camp will be surprised to hear that I enjoyed the three talks of the session better than any of that ilk that I had previously endured. The reason is simple: I took along some interesting reading material and ignored the speakers. That technique served to advantage again for three more snoozers, Thursday’s “digital signature and electronic cash” session, but the final session, also on complexity theory, provided some sensible listening.
more on his blog: http://www.scottaaronson.com/blog/?p=2059
The next Hack Summit will happen entirely online and will start on December the 1st.
https://hacksummit.org/
You can get a free ticket by posting it on twitter/facebook.
An amazing line up of people will be giving talks: David Heinemeier Hansson (creator of Ruby on Rails), Tom Chi (creator of Google Glass), Hakon Wium Le (creator of CSS), Bram Cohen (creator of Bittorrent), Brian Fox (creator of Bash), Hampton Catlin (creator of Sass and Haml), and many more interesting persons and even....... Jon Skeet (#1 answerer on StackOverflow). This is gonna be huge!
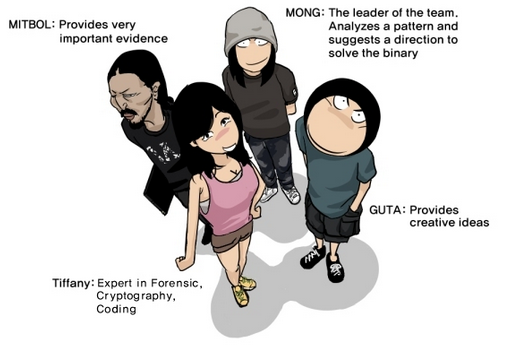
The Sapheads team draw a comic as a write up for the finale of the Defcon CTF in 2009. Since it's a classic here it is
I was in Bucharest for two weeks and look what I ran into!

http://bitcoinromania.ro/
I've run into a nice series of video called "hack of the day" from Vivek-Ramachandran.
In this first video he explains two techniques :
- jump-call-pop
- xor decoding
I also got nice tips like the examining string function in gdb : x/s $ebx or the folder usr/include/asm that contains plenty of information about assembly.
The full playlist can be found on securitytube.net
A new attack on SSL 3.0 has been discovered. It's relevant because most browsers (except for Opera) allow a downgrade to SSL 3.0 if it cannot seem to use newer versions. Of course an attacker could disturb the connection and force someone to use SSL 3.0 in order to use the POODLE attack.
Full and clear explanation here
You might want a reminder of what is CBC to read it:

tl;dr: attack happens because of the way padding works in CBC in SSL 3.0
It's old but I just discovered it! And since it's not always fun to learn a new text editor, especially one like vim, here's a fun way to do just that!

http://vim-adventures.com/
Ken Shirriff, still writing about bitcoin, has found a new hobby: mining bitcoin blocs with only a paper and a pen.




